Multiple brokers on Monday showed signs of falling victim to a hack that saw hundreds of load postings flying onto DAT's load board quicker than the users could delete them, and perhaps even defeating DAT's own revamped security measures.
"It was on Monday," said Tina Giramma, a broker at ST Freight. "I had gotten a couple emails about some random load that's not my load. It happens every now and then." Yet when she "opened up DAT, the whole damn page was full of postings. I kept scrolling and went, 'oh crap,'" before letting the enterprise account holder know someone had gotten into her account.
Giramma is the only user on her account. Yet somehow, other users were simultaneously logged in with a different IP address and posting loads.
"I couldn't delete them fast enough," she said. "As soon as I would delete 150" loads, "150 more would pop up."
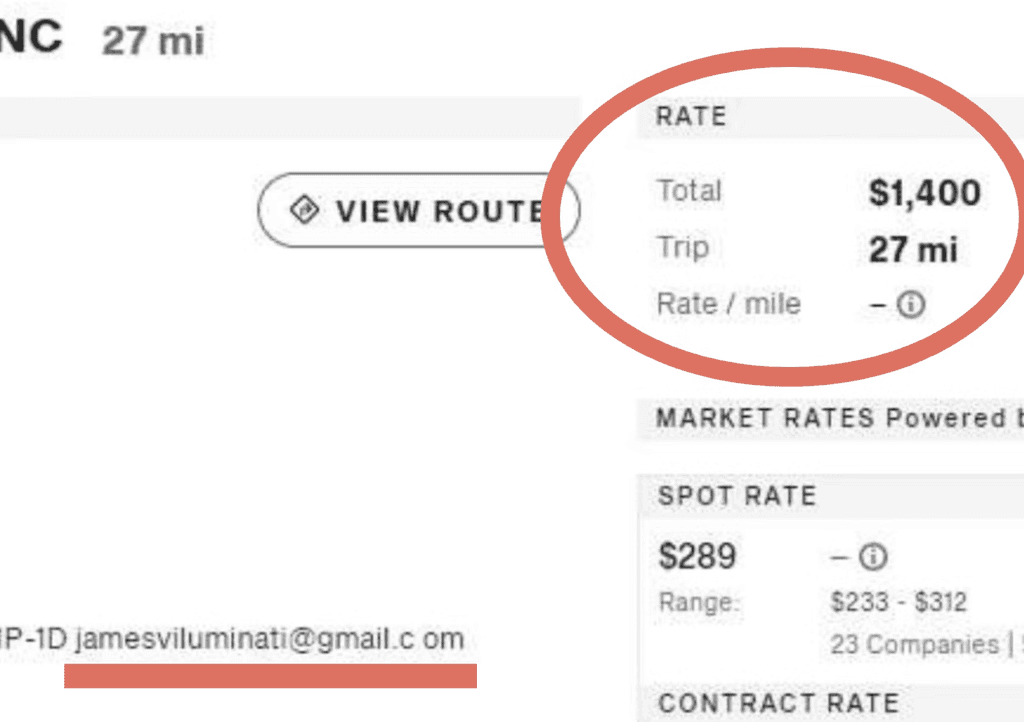
Now Giramma had carriers emailing her about the loads, and some of the postings' more eye-popping details emerged. $1,200 for a 27-mile haul from Charlotte, North Carolina, to nearby Concord, power only, dropping off in a Circle K parking lot. A similar set popped up near Amazon's Kent, Washington, distribution centers.
Everything on the posting showed correctly as an ST Freight load, except for the note in the commodity section that says the email. "The email that they put in there is jamesviluminati@gmail.com. Notice the space in the word com."
Other postings from ST and other brokers had another email address listed, also with the space, but a few did not. In total, likely a few thousand went up across a few brokers.
This scammer's or scammers' mission was to "bulk download hundreds of power only loads. From what I could tell, these are trailer moves from Amazon facilities."
Further research revealed two IP addresses accessing ST's accounts in particular. One VPN address basically presents as untraceable. The other seemed to lead back to Amazon's Boardman, Oregon, data center.
"Possibly an inside job" involving someone with knowledge of Amazon's logistics operations, Abts speculated.
Inside job or not, the hacker here seemed intent to move trailers from an Amazon warehouse to a nearby location — that Circle K parking lot in ST Freight's case, where they might easily be stolen. Despite efforts of carriers, brokers, load boards like DAT and Truckstop and so many others, cargo theft has soared in recent years, up 10% last quarter, 46% year over year, while freight fraud jumped 130% in 2023.
As Giramma frantically deleted the postings coming from the ST Freight accounts, messages from carriers poured in, some identifying the obvious scam and confronting her about it, others just inquiring about the quite profitable load.
"I kept trying to delete as fast as I can, thinking DAT is going to get me shut off immediately," said Giramma. "There should be an option where you can disable your account immediately."
Instead, she said it took an hour and a half for DAT to step in.
Giramma uses two-factor authentication, a tool that's supposed to help keep unauthorized people out of her account, heralded as a big security achievement within the last year by both DAT and Truckstop load board networks.
A simple space bar keystroke seemed to have defeated a piece of DAT's security regime.
Another broker whose account got hacked said that DAT informed them they had fallen for a phishing email. "We got an email from reviews@directory-datone.com saying that we got a bad review on DAT, and I saw in that box it's some carrier I've never worked with." But that email address is fake, and the link it contained led the broker to enter their login credentials, giving the scammer full access despite the two-factor authentication.
Let it be a reminder that such dangers are present — if a load is paying $20/mile, that might be one of those too-good-to-be-true situations worth double checking.